Aggregator vs. Direct EOR Model: Which One Actually Protects You?
Every EOR provider's website says the same thing: compliant hiring in 150+ countries. Simple. Fast. Risk-free. But behind that promise,…
There’s a conversation happening in boardrooms right now that should make every security leader uncomfortable. It goes like this: “We spent $2 million on endpoint protection. We have next-gen firewalls. Our network is locked down. So why are we still getting breached?”
The answer nobody wants to hear is that attackers stopped trying to break through your perimeter years ago. They simply log in with legitimate credentials instead.

According to PwC’s Annual Threat Dynamics 2026 report , attackers are “logging in rather than breaking in” a fundamental shift that renders traditional perimeter defense nearly irrelevant. IBM’s 2026 X-Force index confirms that abuse of user identities was the preferred entry point in 30% of incidents they tracked. Verizon’s Data Breach Investigations Report shows credential abuse accounts for 22% of all breaches, with 88% of attacks in basic web application patterns involving stolen credentials.
Here’s the uncomfortable truth: your employees have become the attack surface. Not because they’re careless or untrained. Because the threat landscape has shifted beneath them, and most organizations haven’t caught up.
In June 2025, security researchers discovered approximately 16 billion login credentials compiled from infostealer malware logs, phishing kits, and prior data breaches. This wasn’t a single company breach – it was an aggregation tied to major platforms including Google, Apple, and Meta.
Infostealer malware alone harvested 1.8 billion credentials in 2025, according to SpyCloud’s Annual Identity Exposure Report 2026. These credentials don’t sit idle in dark web marketplaces. They fuel ransomware operations, business email compromise schemes, and account takeover attacks on an industrial scale.
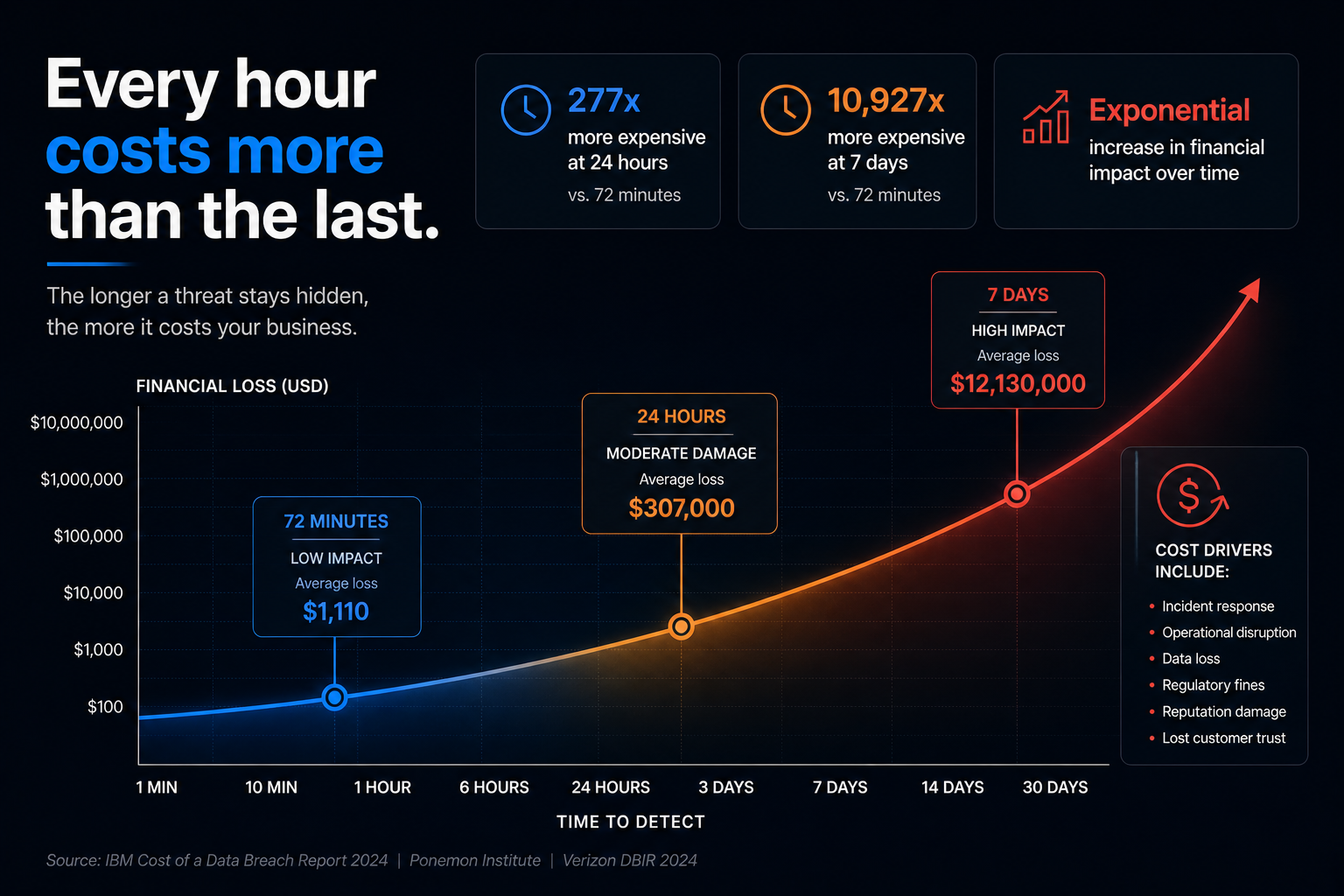
What makes this especially dangerous is the speed of weaponization. Unit 42’s Global Incident Response Report 2026 found that the fastest 25% of intrusions reached data exfiltration in just 72 minutes. Once an attacker has valid credentials, they move with the speed of a legitimate user – because to your systems, they are one.
Most cybersecurity awareness training for employees still focuses on spotting phishing emails based on telltale signs: odd formatting, generic greetings, and slightly wrong sender domains. That training worked when phishing was crude.
AI-generated phishing now routinely passes those checks. According to research tracking 2026 identity threats, AI spear phishing is no longer primarily aimed at credential theft via fake login pages. It’s increasingly used to initiate business email compromise, manipulate OAuth consent flows, and extract session tokens from enterprise tools.
Here’s what changed: attackers realized the credential is often just the first step. The real prize is longer-term identity persistence – staying inside your systems undetected while they map your network, identify high-value data, and establish fallback access points.
SpyCloud’s 2026 report reveals that 49% of phishing victims are corporate users, not consumers. It’s essentially an even split, demonstrating that enterprise security controls alone are not preventing identity compromise. More troubling: 40% of malware infections occurred on endpoints with EDR or antivirus tools installed, showing attackers routinely bypass traditional endpoint defenses to steal identity data.
If you’re thinking “we have MFA enabled, we’re protected,” you’re operating under a dangerous assumption that attackers have already learned to exploit.
MFA fatigue attacks rose 217% year-over-year, according to Verizon’s 2025 DBIR. Push-notification MFA has become a liability in high-risk environments because attackers simply spam authentication requests until the exhausted user approves one to make the notifications stop.

SIM swapping attacks remain devastatingly effective in 2026 because SMS-based one-time passwords are still widely deployed. In a SIM swap attack, the attacker contacts a mobile carrier, impersonates the target using personal information from social media or data broker sites, and convinces the carrier to transfer the phone number to a SIM card they control. Once transferred, any SMS-delivered OTP goes directly to the attacker.
NIST’s guidance on phishing-resistant MFA is explicit: SMS and push notifications are not phishing-resistant. FIDO2 passkeys and hardware security keys are, because they’re origin-bound – even if a user is deceived into visiting a convincing fake login page, the passkey won’t respond because the domain doesn’t match the registered origin.
While security teams focus on protecting human identities, machine identities have multiplied unchecked. Gartner warns that machine identities – API keys, service accounts, automation credentials – now dramatically outnumber human identities and are often completely unmanaged.
These non-human identities don’t get sick, take vacations, or raise suspicion when they access systems at 3 AM. They’re the perfect vehicle for persistent access. A compromised service account can remain active for months or years without anyone noticing unusual behavior.
Unit 42’s incident response data shows identity weaknesses played a material role in almost 90% of investigations, with initial access driven by identity-based techniques in 65% of cases. This includes not just stolen passwords but brute force attempts, insider activity, and the exploitation of poorly managed machine credentials.
The shift from credential-based attacks requires architectural changes, not just training campaigns. Here’s what security leaders should prioritize:
Deploy phishing-resistant authentication universally. Legacy authentication – passwords, SMS OTP, push-based MFA – fails against modern threats by design. Organizations need to transition to FIDO2 passkeys, hardware security keys, or device-bound credentials that cannot be phished, intercepted, or replayed.
Implement Identity Threat Detection and Response (ITDR). Traditional security tools monitor network traffic and endpoint behavior. ITDR specifically watches for anomalies in how identities are used: unusual login times, access to new resources, privilege escalations, or OAuth consent flows that deviate from baseline patterns.
According to researchers analyzing 2026 threats, user behavior cannot be easily counterfeited at scale. The way a legitimate user navigates an application, the rhythm of their keystrokes, decision-making patterns – these behavioral signals provide continuous verification throughout entire sessions rather than just a one-time check at login.
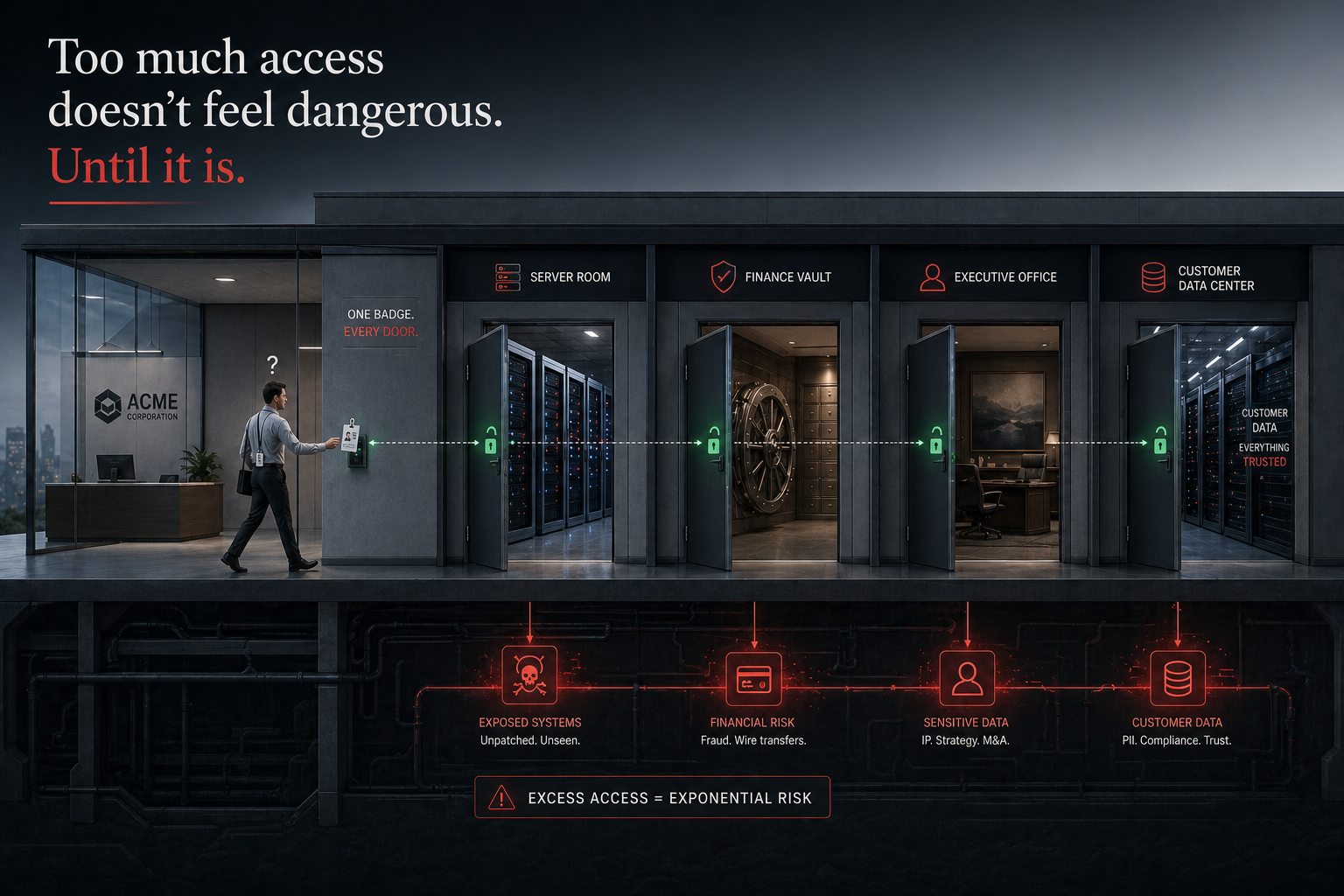
Adopt least-privilege and just-in-time access. Standing access privileges are standing invitations for lateral movement. Zero-standing-privilege architectures grant temporary, scoped access only when needed and automatically revoke it when the task completes. This dramatically reduces the blast radius when credentials are compromised.
Inventory and protect machine identities. Every API key, service account, and automation credential needs the same governance applied to human identities: regular rotation, access logging, anomaly detection, and immediate revocation capabilities.
Compunnel’s identity and access management services provide the unified platform needed to manage both human and machine identities across hybrid environments, with continuous verification and automated response capabilities that match the speed of modern attacks.
Build continuous behavioral monitoring. Static security policies assume normal behavior looks the same every day. Continuous monitoring establishes baseline patterns for each identity and flags deviations in real time. When a finance employee who normally accesses accounting systems during business hours suddenly starts querying customer databases at midnight, that’s a signal worth investigating immediately.
Cyber insurance providers have caught on to the identity crisis. Analysis of denied claims in 2025 found that 82% involved organizations without proper MFA implementation. But “proper” now means phishing-resistant MFA, not just any second factor.
Regulatory frameworks are tightening. The EU’s NIS2 directive mandates Zero Trust as a basic practice of cybersecurity hygiene. NIST’s Zero Trust Architecture guidance is explicit about identity as the foundation. Organizations that treat identity security as optional are increasingly finding themselves uninsurable and non-compliant.
The perimeter security model assumed a clear boundary between trusted internal networks and untrusted external threats. That boundary dissolved with cloud adoption, remote work, and SaaS proliferation. Modern enterprise infrastructure has no meaningful perimeter.
Identity became the new perimeter by default. Every access request – whether from a CEO on their laptop, a contractor using a mobile device, or an API making a service-to-service call – must prove identity, verify context, and receive only the minimum access required.
This isn’t about distrusting employees. It’s about recognizing that credentials can be stolen, devices can be compromised, and sessions can be hijacked. The architecture must assume breach and contain damage, not just prevent entry.
The gap between understanding the identity threat and actually implementing effective controls remains wide. Common failure patterns include:
Tool-first buying without governance change. Vendors sell point solutions labeled “identity security,” but if the underlying access policies remain unchanged, the tools just create visibility into an unchanged attack surface.
Treating identity as an IT project with an end date. Identity security is an ongoing operating model, not a one-time deployment. Configurations drift, environments change, new applications get added, employees join and leave. Without continuous policy enforcement and regular audits, controls degrade over time.
Neglecting the employee experience. Security controls that create excessive friction lead to workarounds. Employees will find ways to bypass authentication systems that make their work harder. The most secure architecture is one that users can actually work within.
Leaving third-party and vendor access unmanaged. The ShinyHunters campaign in 2025 exploited OAuth relationships in Salesforce user environments by granting OAuth access to the Data Loader app, enabling attackers to access victim environments and exfiltrate data using Salesforce’s own tooling. Third-party integrations are trusted pathways that attackers actively target.
CISOs often struggle to secure budget for identity initiatives because the return on investment isn’t immediately visible. The cost of a breach is obvious in retrospect. The cost of breaches prevented is invisible.
Frame identity security investment in terms of:
Reduced breach impact. Organizations with mature identity and access management cut mean time to detect and respond by 60% according to enterprise security benchmarks. Faster detection means lower exfiltration, less ransomware spread, and reduced recovery costs.
Insurance and compliance savings. Demonstrating phishing-resistant MFA, ITDR capabilities, and continuous monitoring directly reduces cyber insurance premiums and accelerates compliance attestation processes.
Operational efficiency. Automated provisioning, just-in-time access, and self-service password reset reduce help desk burden while improving security posture. The business case isn’t security versus productivity – it’s security enabling productivity.
Your employees haven’t become the attack surface because they’re doing anything wrong. They’ve become the attack surface because attackers optimized their methods against the weakest architectural link, and most organizations are still defending a perimeter that no longer exists.
The shift to identity-first security isn’t optional anymore. It’s the foundational requirement for operating in a world where credential theft drives 22% of breaches and attackers move from initial access to data exfiltration in under 72 minutes.
Security leaders who recognize this shift and act now – implementing phishing-resistant authentication, deploying ITDR, managing machine identities, and building continuous verification into every access request – will be the ones who can confidently answer that boardroom question: “Why are we still getting breached?”
The answer will be: “We’re not. Because we stopped defending the wrong perimeter.”
Your identity infrastructure might already be compromised – and traditional tools won’t tell you. Compunnel’s cybersecurity services provide comprehensive identity threat assessment, phishing-resistant authentication deployment, and continuous behavioral monitoring that matches the speed of modern attacks. Our experts help organizations transition from perimeter-based to identity-first security without disrupting business operations. Schedule a security assessment to discover your identity exposure before attackers do.
