Aggregator vs. Direct EOR Model: Which One Actually Protects You?
Every EOR provider's website says the same thing: compliant hiring in 150+ countries. Simple. Fast. Risk-free. But behind that promise,…
There’s a moment that defines every CISO’s tenure – the audit that reveals employees across cloud environments, personal devices, and contractor networks are all operating under the same implicit trust assumption: if you’re inside the network, you’re trusted. In 2026, that assumption is actively dangerous.
84% of organizations experienced an identity-related breach in 2025. The average cost reached $5.2 million per incident. In the United States, the average breach cost surged to $10.22 million – the highest worldwide. (Startup Defense / Entrust, 2026)
In 75% of cases, attackers didn’t break through the perimeter – they simply logged in using stolen credentials. They walked through the front door. Zero Trust Architecture (ZTA) is the structural answer. Every user, device, and application must prove their identity and authorization before accessing any resource and must continue to do so throughout the session.
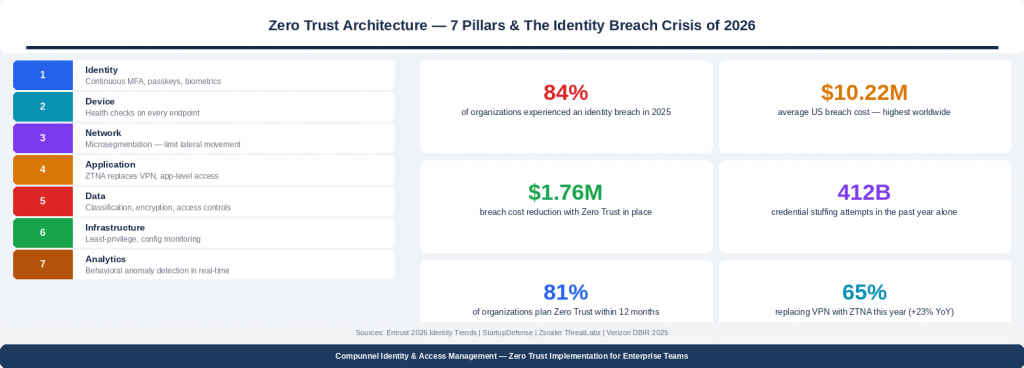
Three forces have driven Zero Trust from strategic aspiration to operational imperative in 2026:
– The credential crisis: 412 billion credential stuffing attempts were recorded in the past year alone. Without Zero Trust controls, a single stolen password can compromise an entire organization.
– The cloud and hybrid work explosion: today’s employees access sensitive data from personal devices, home networks, and airports. There is no perimeter left to defend.
– The financial case: organizations without Zero Trust implementation face breach costs 38% higher than those with it. Zero Trust reduces breach costs by an average of $1.76 million per incident.
1) Human identities: Every employee, contractor, and partner must be continuously verified. Passwordless authentication via passkeys and biometrics is rapidly becoming the industry standard, eliminating the credential-theft vector at its source.
2) Machine identities: Application Programming Interfaces (APIs), microservices, Continuous Integration/Continuous Delivery (CI/CD) pipelines, and automated workflows all require credentials. Most enterprises have far more machine identities than they realize – and far less visibility into them.
3) AI agent identities: Autonomous AI systems that call APIs, access data stores, and interact with external services require their own access management discipline. Most enterprise security frameworks have not yet addressed this surface.
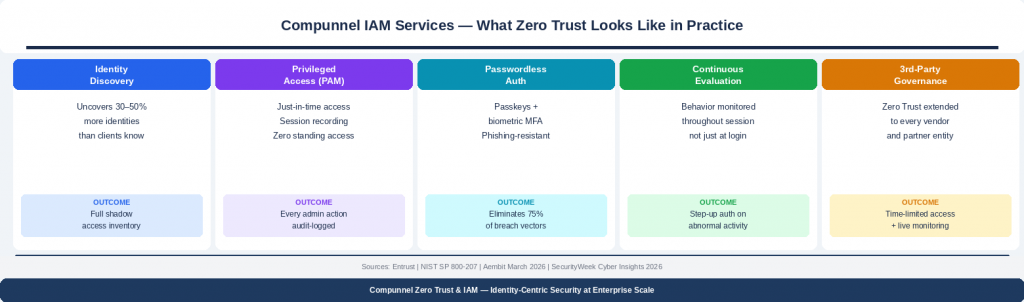
Compunnel’s Identity and Access Management Services
– Identity Discovery: Typically uncovers 30–50% more identities than clients believe they have, and a corresponding number of unmanaged access credentials.
– Privileged Access Management (PAM): Just-in-time access provisioning, session recording, zero standing privileged access – Every administrative action is audit-logged.
– Passwordless Authentication: Phishing-resistant Multi-Factor Authentication (MFA), passkeys, and biometric verification – Eliminates the vector behind 75% of all breaches.
– Continuous Access Evaluation: Behavioral monitoring throughout each session – anomalous patterns trigger immediate step-up auth or session termination.
– Third-Party Identity Governance: Zero Trust principles applied to every vendor and partner, including time-limited access grants and continuous activity monitoring.
Is your identity security posture Zero Trust ready?
Request a complimentary Identity Risk Assessment | compunnel.com/cybersecurity
