AI-Powered EOR: How Real-Time Compliance Monitoring Reduces Risk
For most of the EOR industry's existence, compliance has been a periodic event. Quarterly reviews. Annual audits. Contract updates triggered…
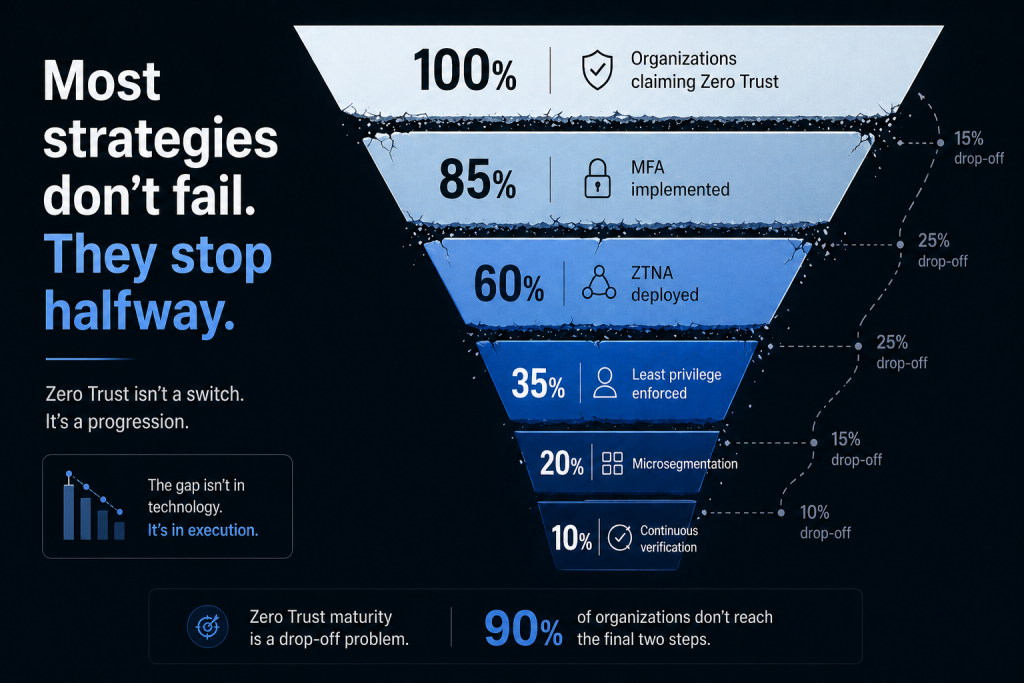
Three years ago, your board approved a Zero Trust initiative. You deployed multi-factor authentication. You implemented a zero-trust network access gateway. You check the “Zero Trust” box on RFPs and compliance questionnaires.
And when the security assessment came back, the finding was stark: you have Zero Trust in name only. The architecture that grants access has fundamentally not changed.
This pattern is so common it has a name in security circles: “Zero Trust washing.” Organizations deploy tools marketed as Zero Trust solutions while leaving the underlying access model completely unchanged. Then they wonder why the promised security improvements never materialize.
According to SecurityWeek’s Cyber Insights 2026 analysis, too many organizations stop at MFA or single sign-on and mistake access control for Zero Trust. The danger isn’t being incomplete – it’s being inconsistent, creating pockets of strict verification alongside wide-open implicit trust.
Let’s talk about why this happens and what actually works.
After examining dozens of stalled Zero Trust initiatives, a clear set of failure patterns emerges:
The most common failure starts in procurement. A vendor demos a Zero Trust Network Access (ZTNA) solution. It looks impressive. It provides secure remote access without a VPN. The purchase gets approved.
Except ZTNA is a delivery mechanism, not a strategy. It securely delivers access based on policies. If your policies still say “anyone in the IT department can access everything in the server room,” ZTNA just securely delivers that problematic access.
Security leaders in banking describe this as “Zero Trust in name only” – an MFA deployment, a ZTNA gateway, but no change in how privileged access or vendor connectivity is actually governed. The tool works perfectly. The architecture remains vulnerable.
Organizations approach Zero Trust like a network upgrade: define scope, deploy technology, complete the project, move on.
Zero Trust isn’t a project. It’s an architectural strategy that requires ongoing operation. NIST’s Zero Trust Architecture guidance (SP 800-207) is explicit: Zero Trust is a set of principles, not a product category. It’s a destination that requires a continuous journey.

Treating it as a project with an end date means configurations drift over time, new applications get added without Zero Trust controls, and the security posture degrades back to implicit trust. One security researcher noted, “Most organizations only start working toward Zero Trust after an auditor, insurance requirement, or compliance standard forces them to. That approach misses the point. When security becomes about passing an audit, companies start checking boxes instead of changing habits.”
Leaders unfamiliar with Zero Trust implementation often assume it’s primarily a technical challenge. Deploy some software, configure some policies, done.
The reality: Zero Trust requires technological change AND organizational change across six critical pillars (identity, devices, networks, applications, data, and automation/orchestration). Each pillar demands expertise in specialized domains. Widespread skill gaps compound the problem – implementing Zero Trust across these pillars requires expertise in identity management, network architecture, data classification, application security, and increasingly, AI and automation.
Unrealistic timelines exhaust budgets and drain resources. Hasty execution creates new vulnerabilities instead of reducing existing ones. According to the analysis of implementation failures, underestimating Zero Trust poses two major risks: derailed project planning from unrealistic expectations and flawed execution that actually defeats the purpose of Zero Trust architecture.
Organizations map out their modern infrastructure – cloud applications, SaaS platforms, mobile access – and design a comprehensive Zero Trust architecture. Then they exempt legacy systems “temporarily” because those systems can’t support modern authentication.
The exemptions become permanent. Core banking platforms, mainframes, industrial control systems, and third-party vendor connections sit outside the Zero Trust architecture. Attackers, being rational, target exactly those exemptions.
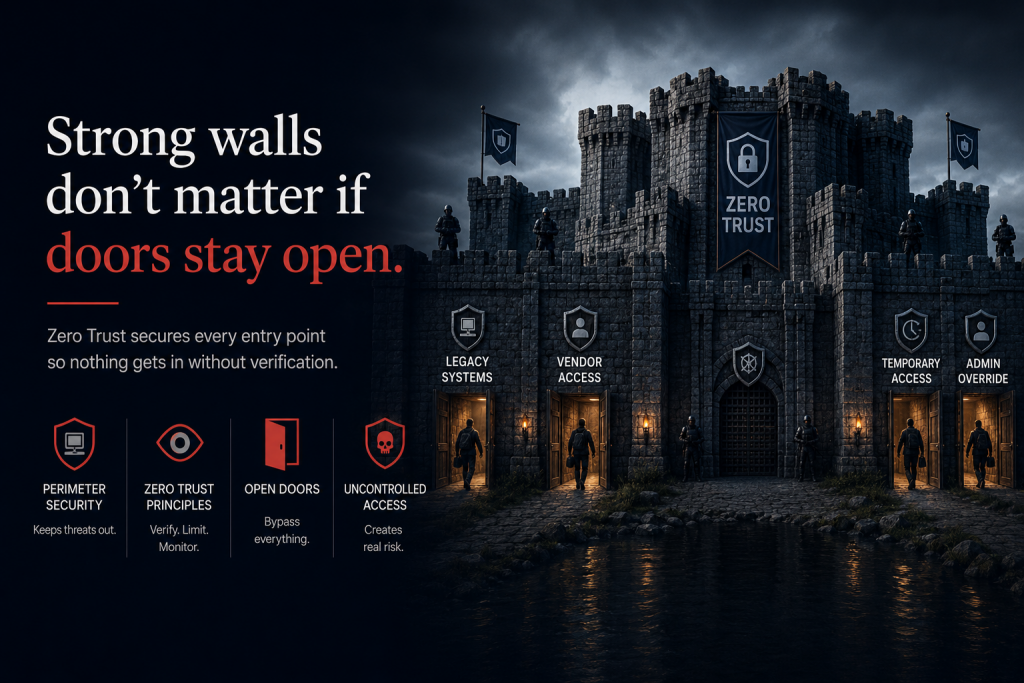
The ShinyHunters campaign in 2025 demonstrated this pattern perfectly. Organizations had implemented Zero Trust for direct access, but granted broad OAuth permissions to third-party applications. Attackers exploited those OAuth relationships to access Salesforce environments and exfiltrate data using Salesforce’s own Data Loader tool. The Zero Trust architecture was technically sound. The architectural blind spot was fatal.
One of Zero Trust’s core principles is continuous verification. Yet many implementations reduce this to: verify once at login, then trust for the duration of the session.
This creates a dangerous gap. An employee authenticates from their office, gets verified, and receives 8 hours of trusted access. Two hours later, they leave their laptop unattended at a coffee shop. An attacker sits down at the unlocked screen. Every system sees “verified 2 hours ago” and grants access.
Continuous verification means exactly that – continuous. Context changes (location, device health, network, behavior) should trigger re-verification. Most implementations verify once and then grant standing access, defeating the “never trust, always verify” principle.
Zero Trust impacts how every employee accesses every resource. That scope requires coordinated action from IT, security, compliance, business units, and executive leadership.
Instead, it typically gets assigned to the security team as a security project. Security can’t change business processes. They can’t dictate how departments access applications. They can’t enforce identity governance without business unit buy-in.
Without clear ownership across CIO, CISO, CRO, and business units, Zero Trust becomes a security initiative that business teams route around whenever it creates friction. Users find workarounds. Shadow IT proliferates. The architecture gets undermined by organizational resistance.
Ironically, the perfect becomes the enemy of the good. Organizations realize Zero Trust is a multi-year journey requiring substantial change. They conclude: if we can’t do it completely, we shouldn’t start at all.
This is backward. Partial Zero Trust implementation – done intentionally and with awareness of gaps – provides meaningful protection. Implementing least-privilege access reduces lateral movement. Segmenting networks contains breaches. Deploying MFA prevents credential replay attacks.
The danger isn’t incompleteness. It’s an inconsistency and false security. Partial implementation creates value as long as you know what remains unprotected. The problem occurs when organizations implement one pillar and declare the entire architecture “Zero Trust” without understanding the gaps.
Understanding failure patterns only helps if you know what success looks like. Here’s what Zero Trust implementation actually requires:
Every Zero Trust journey starts with the same foundational question: Can you verify every subject’s identity with confidence? Until you can definitively answer that question, everything built on top will have a weak foundation.
This means moving beyond passwords to phishing-resistant authentication. It means managing both human identities (employees, contractors, partners) and machine identities (service accounts, API keys, automation credentials). It means integrating identity verification into every access decision across every system.
Identity and access management becomes the control plane for Zero Trust. Strong identity verification doesn’t guarantee security, but weak identity verification guarantees eventual compromise.
Zero Trust means granting the minimum access required for the minimum duration needed. This directly contradicts how most organizations currently operate: grant broad access at hire, never revoke until termination.
Least-privilege means a finance employee can access accounting systems during business hours from managed devices. They can’t access engineering repositories. They can’t authenticate at 3 AM. Their access automatically revokes when they transfer departments.
Just-in-time means a developer who needs to debug production receives temporary elevated access for 2 hours, then automatically loses it. Standing administrative privileges are standing invitations for lateral movement.
Implementing this requires automated provisioning, continuous policy enforcement, and integrated access management across every system – cloud, on-premise, SaaS, and legacy.
Network segmentation has existed for decades. Microsegmentation takes it further: every application, every workload, every data store becomes its own security zone. Breaching one zone doesn’t grant access to anything else.
This stops lateral movement, the primary technique attackers use after initial access. With microsegmentation, an attacker who compromises a web server can’t pivot to databases, file servers, or identity systems. They’re contained in a zone that provides nothing useful.
The challenge is that microsegmentation requires understanding application dependencies, data flows, and trust relationships. Organizations often discover their architecture is far more interconnected than they realized. Documenting these dependencies becomes a prerequisite for effective segmentation.
Static policies verify identity once. Continuous monitoring is verified throughout the entire session. Is the authenticated identity behaving normally? Are they accessing resources consistent with their role? Has the device context changed?
User and Entity Behavior Analytics (UEBA) establishes baseline patterns and flags deviations. This catches compromised credentials that passed initial authentication, insider threats, and account abuse.
Compunnel’s security operations services provide the continuous monitoring infrastructure needed for Zero Trust. Rather than periodic security assessments, security operations correlate real-time telemetry across identity, endpoints, network, and cloud to detect policy violations and behavioral anomalies as they occur.
The exemptions will kill you. Legacy systems that can’t support modern authentication. Vendor connections that need broad access. Partner integrations are built on standing trust relationships.
These can’t be ignored. They need explicit risk acceptance, compensating controls, and plans for remediation. If a legacy system can’t do MFA, it goes behind a privileged access management solution that CAN do MFA. If a vendor needs access, it’s time-limited, monitored, and scoped to exactly what they need.
Third-party risk in Zero Trust means every partner connection gets the same treatment as employee access: verified identity, least privilege, continuous monitoring, and automatic revocation.
Organizations can’t pause operations to implement Zero Trust. Transformation must occur while systems remain in production. This creates tension between operational continuity and architectural change.
The practical approach is a phased implementation starting with the highest-risk systems. Protect crown jewels first – customer data, intellectual property, financial systems – then expand outward. This delivers security value immediately while building toward comprehensive coverage.
Compunnel’s cyber strategy services help organizations design phased Zero Trust roadmaps that balance security improvement with business continuity. Rather than attempting enterprise-wide transformation simultaneously, strategic planning identifies high-impact controls that can be implemented without disrupting critical operations.
Configurations drift. Environments change. New threats emerge. Zero Trust requires ongoing maintenance to remain effective.
This means automated policy validation, regular architectural reviews, continuous training, and proactive threat modeling. Without this, even a perfect Zero Trust architecture degrades over time as policies accumulate exceptions, new systems get added without proper integration, and organizational changes bypass security governance.
Technical implementation is only half the challenge. Zero Trust requires organizational transformation.
Business units will resist when access becomes more restrictive. Developers will complain when just-in-time access creates friction. Legacy application teams will argue their systems can’t support modern authentication.
These aren’t technical problems to solve with better tools. They’re organizational problems requiring executive sponsorship, change management, and willingness to say “this access model is fundamentally insecure and must change even if it’s inconvenient.”
The cybersecurity talent shortage makes this worse. Finding professionals who understand Zero Trust architecture, can implement it across multiple technical domains, and have the communication skills to drive organizational change is extraordinarily difficult.
This reality is driving the adoption of managed security services and strategic partnerships. Rather than trying to build internal expertise across every Zero Trust pillar, organizations partner with providers who have already solved these problems and maintain specialized teams.
Zero Trust has no finish line. There’s no moment when you can declare “Zero Trust implementation complete.” The threat landscape evolves. Your infrastructure changes. Attackers develop new techniques.
Instead of completion, measure maturity and continuous improvement:
Verification coverage: What percentage of access requests require verification? What percentage are still implicitly trusted?
Mean time to verify: How long does identity verification take? Is it creating unacceptable friction?
Policy enforcement consistency: Are policies applied uniformly, or do exceptions exist? Are those exceptions documented and risk-accepted?
Incident containment: When breaches occur, does microsegmentation contain them or can attackers move laterally?
Behavioral detection rate: What percentage of compromised credentials are detected through behavioral monitoring rather than after damage occurs?
These metrics show whether you’re moving toward Zero Trust or just deploying products that claim to enable it.
Most Zero Trust initiatives fail not because the concept is flawed but because implementation treats it as a product purchase instead of an architectural transformation.
You can’t buy Zero Trust from a vendor. Vendors sell components that enable Zero Trust: identity verification platforms, microsegmentation tools, ZTNA gateways, and policy engines. But Zero Trust is how you architect those components together with clear governance, continuous verification, and least-privilege principles.
The organizations succeeding with Zero Trust are those who: – Understand it’s a multi-year architectural journey, not a project – Start with identity verification as the foundational control – Phase implementation to protect high-value assets first – Accept that legacy systems need compensating controls, not exemptions – Invest in continuous monitoring and behavioral analytics – Maintain executive sponsorship across IT, security, and business units.
The organizations failing are those who deploy a ZTNA product, enable MFA, and declare victory while leaving the underlying implicit trust architecture completely unchanged.
Which approach describes your organization?
Your Zero Trust initiative stalled because you started with products instead of architecture. Compunnel’s cyber strategy services provide the expertise needed to design, phase, and implement a genuine Zero Trust architecture aligned with your business operations. We help organizations move from checkbox compliance to operational Zero Trust that actually reduces breach risk. Our security architects have implemented Zero Trust across finance, healthcare, and enterprise IT environments. Schedule a Zero Trust assessment to understand your current maturity and create a phased roadmap that delivers security value without disrupting operations.
