AI-Powered EOR: How Real-Time Compliance Monitoring Reduces Risk
For most of the EOR industry's existence, compliance has been a periodic event. Quarterly reviews. Annual audits. Contract updates triggered…
Your identity and access management system tracks every employee. You know who has access to what. You enforce password policies, MFA requirements, and regular access reviews. Your IAM governance is strong.
Except you’re governing the minority of identities in your environment. For every human identity, there are roughly ten machine identities – API keys, service accounts, automation credentials, OAuth tokens – and most organizations have no idea where they are or what they can access.
Gartner’s stark warning: machine identities now dramatically outnumber human identities and are often completely unmanaged. While security teams implement sophisticated controls for employees, machine identities proliferate unchecked with standing privileges, no rotation schedules, and no monitoring.

This isn’t a theoretical gap. It’s the entry point attackers are actively exploiting.
Machine identities are non-human credentials that allow systems, applications, and automated processes to authenticate and access resources. They include:
Service accounts that run applications and background processes with their own credentials
API keys that authenticate application-to-application communication
OAuth tokens that grant delegated access between services
SSH keys that enable automated system access without passwords
Cloud IAM roles and policies that grant cloud resources access to other cloud resources
Certificate-based authentication for system-to-system encrypted communication
Webhook secrets that verify automated notifications between systems
Every modern application depends on dozens or hundreds of these machine identities to function. Microservices architecture, CI/CD pipelines, cloud-native development, and API-first design have accelerated their proliferation exponentially.
The problem: while humans are hired, onboarded, reviewed quarterly, and eventually offboarded, machine identities get created during deployment and forgotten. They accumulate over time with no governance, no expiration, and frequently, no owner who remembers creating them.
From an attacker’s perspective, machine identities are ideal for persistence and lateral movement.
They don’t get sick or take a vacation. A compromised service account can run commands 24/7 without raising behavioral flags the way compromised human credentials would.
They often have elevated privileges. Application service accounts frequently run with administrator rights. Cloud IAM roles grant broad permissions to entire categories of resources.
They rarely get rotated. According to Verizon’s Data Breach Investigations Report, unmanaged devices and credentials were behind 46% of compromised systems. Machine credentials often go years without rotation, while human passwords face 90-day expiration policies.
Usage patterns don’t trigger behavioral alerts. When a human account accesses systems at 3 AM on Sunday from a new location, that’s anomalous. When a service account does exactly that, it’s normal operation. Behavioral detection tuned for human patterns misses machine credential abuse entirely.
They survive user offboarding. When an employee leaves, their account gets disabled. The service accounts they created often remain active indefinitely. Attackers love credentials that outlast the people who can report them compromised.
SpyCloud’s 2026 Identity Exposure Report found that attackers are increasingly targeting non-human identities (NHIs), including API keys, tokens, and service accounts, as high-value targets alongside password managers and AI tools. These provide persistent access that doesn’t depend on phishing users or bypassing MFA.
The first challenge in machine identity management is simply discovering them. Most organizations have no comprehensive inventory.

Ask your security team: how many service accounts exist across your environment? Where are all the API keys that can access your production systems? Which OAuth tokens grant third-party applications access to internal data?
The honest answer is usually: we don’t know.
Machine identities get created by: – Developers during feature development – DevOps teams in CI/CD pipelines.
– Cloud deployments through infrastructure-as-code – SaaS integrations during application configuration – Automation scripts written years ago – Legacy systems migrated from on-premise
They live in: – Active Directory and LDAP – Cloud IAM systems (AWS, Azure, GCP) – Application configuration files – Container orchestration platforms – Secrets management vaults (if you’re lucky) – Source code repositories (if you’re not) – Plain text in scripts and config files (if you’re really unlucky)
Conducting a comprehensive machine identity inventory requires scanning configuration management databases, application deployment scripts, container images, cloud IAM configurations, and source code repositories. Few organizations have done this systematically.
Without inventory, governance is impossible. You can’t review access you don’t know exists. You can’t rotate credentials you can’t find. You can’t detect anomalous usage of identities you aren’t monitoring.
Human identities follow a defined lifecycle: provision at hire, modify during role changes, review quarterly, and deprovision at termination. Identity and access management platforms enforce this lifecycle with automated workflows.
Machine identities typically have no lifecycle at all. They get created when needed and persist indefinitely. There’s no review process. No automatic expiration. No owner accountability.
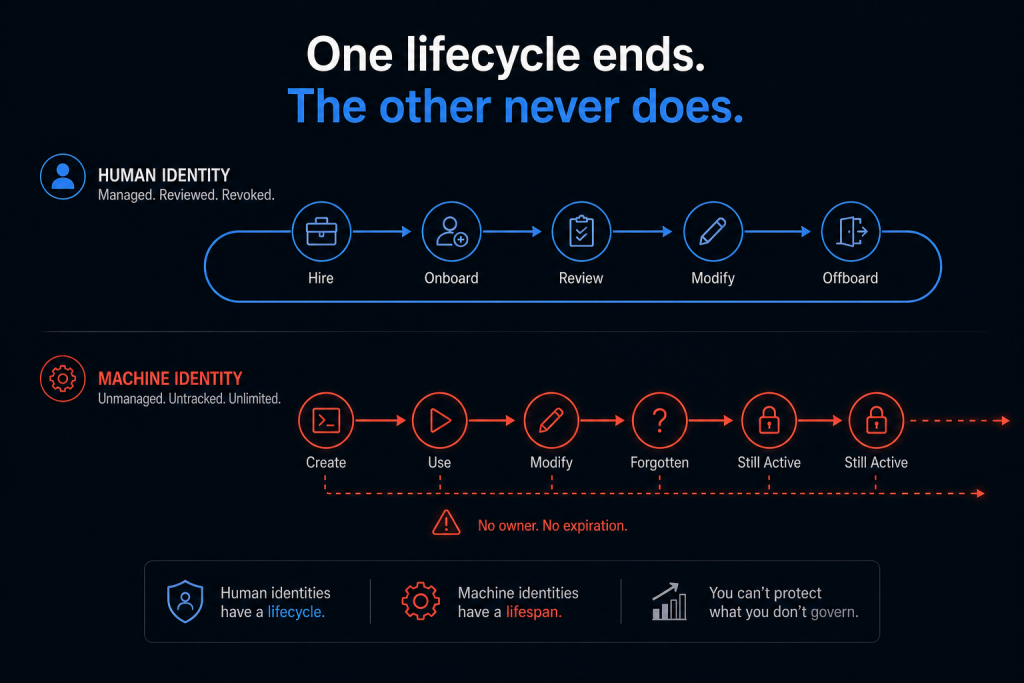
This creates several dangerous conditions:
Credentials that should be temporary become permanent. A developer creates an API key for testing. It works. The key gets checked into the application code and shipped to production. Years later, that test credential – with overly broad permissions created for convenience – still grants production access.
Orphaned credentials accumulate. Applications get decommissioned. DevOps engineers change teams. Automation scripts get deprecated. The credentials associated with all these remain active, with nobody responsible for them.
Privileges escalate over time. A service account starts with minimal access. Requirements change. Rather than create a new account with appropriate scope, someone adds permissions to the existing account. This happens repeatedly until the service account has effectively unlimited access.
Effective identity and access management services must extend lifecycle management to machine identities with the same rigor applied to human accounts: automated discovery, regular access reviews, privilege minimization, mandatory rotation schedules, and automated deprovisioning when no longer needed.
Where organizations store machine credentials matters enormously.
Best case: credentials live in dedicated secrets management platforms (HashiCorp Vault, AWS Secrets Manager, Azure Key Vault) with access controls, encryption, automatic rotation, and audit logging.
Common case: credentials live in application configuration files, environment variables, and configuration management systems with minimal protection.
Worst case: credentials are hardcoded directly in application source code and checked into version control, where they’re accessible to anyone with repository access and persist in git history even after deletion.
SpyCloud’s research confirms this problem is widespread. They track exposed identity data from multiple sources, including malware infections and code repositories. Machine credentials leak at a significant scale through compromised CI/CD pipelines, exposed configuration files, and committed secrets in source code.
The challenge is operational: applications need credentials to function. Those credentials must be retrievable by the application at runtime. Striking the balance between security and functionality requires a secrets management infrastructure that most organizations haven’t deployed systematically.
Machine identities frequently have excessive permissions because limiting scope is technically difficult.
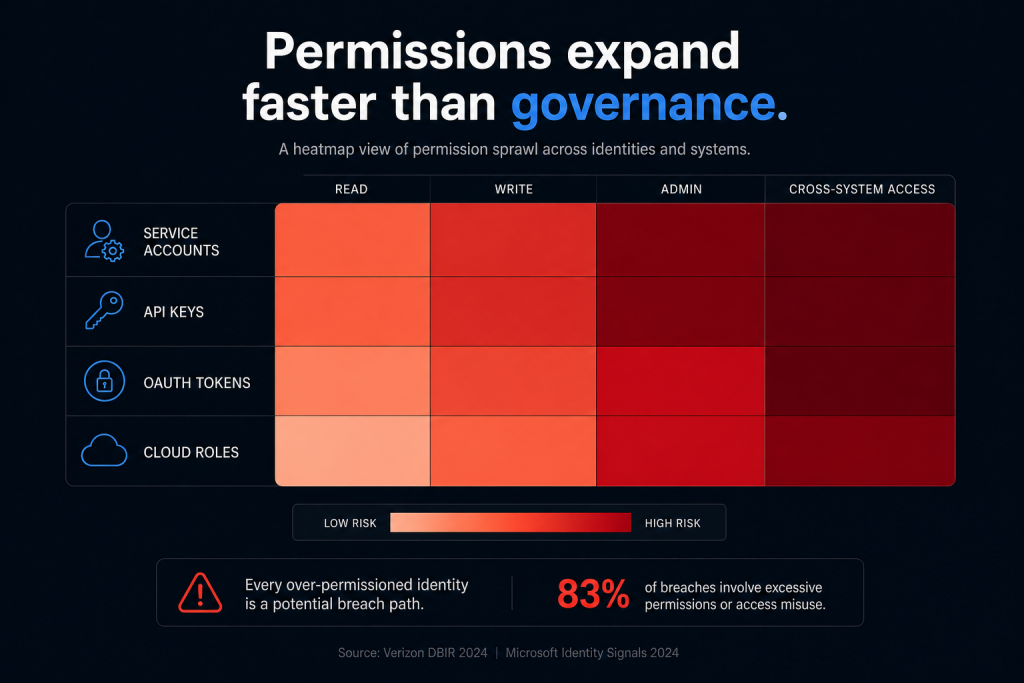
A cloud service account needs read access to one S3 bucket. The path of least resistance is granting read access to all S3 buckets. Writing least-privilege IAM policies requires understanding exact resource requirements, spending time on policy debugging, and maintaining those policies as requirements change.
Multiply this across thousands of service accounts and API keys, and permission sprawl becomes endemic. Most machine identities operate with far more access than they require.
This violates Zero Trust principles spectacularly. When a service account with read access to “all databases” gets compromised, the attacker inherits that excessive access. Least privilege means scoping permissions to exactly what’s needed and nothing more.
Compunnel’s approach to identity and access management includes automated permission rightsizing for machine identities – analyzing actual usage patterns to identify unused permissions and recommending least-privilege policies based on observed behavior rather than declared requirements.
Behavioral analytics work well for human identities because normal behavior has patterns. You work certain hours. Access certain systems. Have predictable geographic locations.
Machine identities don’t have these patterns. A service account might legitimately access systems at any hour from any location. Usage volume can spike dramatically during normal operations. Geographic distribution is normal for cloud services.
This makes anomaly detection much harder. What signals indicate a compromised machine identity versus a legitimate usage spike?
Effective detection requires understanding the specific context of each machine identity: – What resources should this identity access? – When should access occur? – What volume is normal? – Are there changes to the identity itself (permission grants, credential rotation)?
Unit 42’s Global Incident Response Report shows identity weaknesses played a material role in 90% of investigations. Many of these involved machine credentials that were compromised but generated no alerts because usage appeared normal.
Security operations need machine-identity-specific detection rules, not just human-behavior baselines. Compunnel’s security operations services include specialized monitoring for non-human identity usage patterns that traditional SIEM rules miss.
The machine identity problem compounds when third-party integrations are involved.
Every SaaS application you integrate with internal systems requires authentication. That’s typically an OAuth token or API key granting the third party access to your data. How many third-party apps have active OAuth grants in your environment? What data can they access? When was that access last reviewed?
The average enterprise uses 200-300 SaaS applications. Each integration creates machine identities. The ShinyHunters campaign in 2025 exploited exactly this: OAuth permissions granted to a legitimate Salesforce tool (Data Loader) were used to access and exfiltrate data. The OAuth token was legitimate. The access was authorized. The usage was malicious.
Third-party integration governance requires: – Inventory of all OAuth grants and API access – Regular review of what third parties can access – Immediate revocation when integration is no longer needed – Monitoring of third-party usage for anomalous patterns
Most organizations lack all of these controls for third-party machine identities.
Closing the machine identity gap requires systematic approach:
Automated discovery and inventory. Use tools that scan Active Directory, cloud IAM, configuration files, container platforms, and code repositories to identify every machine credential in your environment. Maintain continuous inventory as new credentials get created.
Centralized secrets management. Migrate credentials out of configuration files and source code into dedicated secrets managers with encryption, access controls, audit logging, and automatic rotation capabilities.
Least-privilege by default. Every machine identity starts with minimal permissions. Additional access requires explicit justification and approval. Regularly review permissions against actual usage and rightsize automatically.
Mandatory rotation schedules. Machine credentials rotate on defined schedules (30, 60, or 90 days depending on risk). Automated rotation eliminates operational burden while reducing exposure window for compromised credentials.
Machine identity lifecycle management. Every machine identity has an owner, purpose, and expiration. When the purpose ends, the identity gets automatically deprovisioned. Regular reviews identify orphaned credentials.
Specialized monitoring rules. Behavioral detection tuned for machine identity patterns rather than human behavior. Alert on permission changes, credential modification, access to new resources, or usage patterns inconsistent with the identity’s purpose.
Your IAM program isn’t complete if it only governs human identities. Machine identities are the majority of credentials in modern enterprises, yet they operate with minimal governance and extensive privileges.
Attackers know this. Gartner knows this. Cyber insurance providers increasingly know this. The only question is: when will your organization treat machine identity management with the same rigor applied to employee access?
The gap won’t close by accident. It requires intentional effort to discover, govern, and monitor the non-human identities your systems depend on. Organizations that close this gap dramatically reduce their attack surface. Those that don’t are leaving the keys to the kingdom scattered across their infrastructure in credentials nobody is watching.
Most organizations have 10x more identities than they think – and 90% aren’t governed. Compunnel’s identity and access management services provide comprehensive machine identity discovery, lifecycle management, automated rotation, and specialized monitoring. We help organizations extend IAM governance to non-human identities with the same rigor applied to employees. Schedule a machine identity assessment to discover how many unmanaged credentials exist in your environment and implement systematic governance before attackers exploit them.
