Every Nurse Who Left Last Quarter Still Has System Access. Do You Know How Many?
A Number That Should Keep Every Healthcare CISO Awake Think of it as digital sediment. Every employee who joined and…
In August 2024, Michigan’s McLaren Health Care went dark. Ransomware. Patient systems compromised. Clinical workflows are thrown into chaos. The Inc Ransom group claimed responsibility. The breach ran from July 17 to August 3, with the full scope not understood until May 2025, when 743,131 patient records were confirmed exposed.
Then it happened again.
The same hospital system. The second ransomware attack in two consecutive years. Same sector, same pain, same fundamental question hanging in the air: if they survived the first one, why didn’t they fix what let the attackers in?
The answer, to anyone who studies breach patterns, is uncomfortable but familiar. They recovered. They did not transform. And when attackers came back, the door they had relied on the first time around was still unlocked.
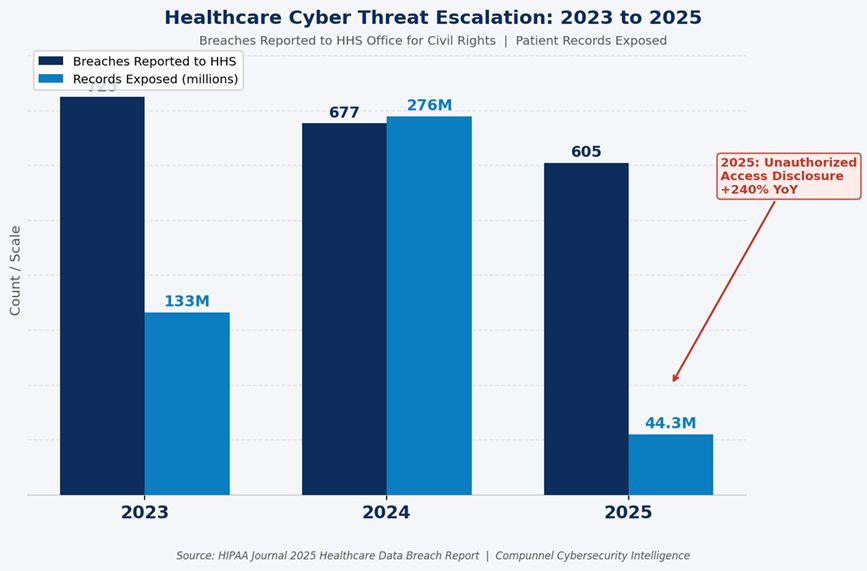
McLaren is not an anomaly. It is a mirror. In 2025, 605 healthcare breaches were reported to the U.S. Department of Health and Human Services, affecting 44.3 million Americans, according to HIPAA Journal’s 2025 healthcare data breach report. Total breach volume surpassed 2024 by 112%. Hacking and IT incidents alone grew 98% year over year. And unauthorized access disclosure — the category that maps most directly to identity failures — jumped a staggering 240%. If there is a single signal inside that data, it is this: the perimeter fell years ago. What is being attacked now is identity.
There is a myth that runs deep in healthcare security planning. The myth says breaches come from the outside. A shadowy attacker, a dark web forum, a nation-state actor. The reality is considerably closer to home.
Privileged credential misuse is the starting point for 74% of data breaches globally. A healthcare staff member clicks on a phishing email. A contractor still has access to a clinical system from a project completed six months ago. A departing administrator’s account was never deprovisioned. An IT vendor retains login credentials to a billing platform that has since been upgraded.
None of these scenarios requires a sophisticated attacker. Every single one of them requires only that your Identity and Access Management controls were incomplete, outdated, or entirely absent. And in healthcare, the average time to identify and contain a breach in 2025 was 241 days, according to Cobalt’s healthcare cybersecurity statistics. Nearly eight months of undetected access. Eight months during which a compromised credential or an orphaned account became the quiet highway through your most sensitive systems.
The average cost of a healthcare data breach in 2026 stands at $7.42 million per incident, the costliest of any industry. The number of healthcare providers reporting losses exceeding $200,000 quadrupled between 2024 and 2025. These are not abstract statistics. They represent ransoms paid, lawsuits settled, reputations rebuilt, and patients who lost trust in the institutions supposed to protect their most personal information.
If you run cybersecurity for a bank or a technology company, access management is complex. If you run it for a hospital, it is a different category of problem entirely.
A nurse does not stay in one department. A physician consults across specialties, systems, and facilities. A traveling clinician arrives on Monday, completes an assignment, and should have their access fully revoked by Friday. Contractors come in to service medical devices and need granular access to specific systems for a specific window of time. Emergency scenarios require instant privilege escalation for staff who do not normally hold it.
Every one of these scenarios is an identity lifecycle event. Every one of them is an opportunity for a misconfiguration, a delayed deprovisioning, or an access creep that leaves a credential in circulation longer than any security team intended. This is why the Joiner, Mover, Leaver process — the disciplined governance of access across the full employment lifecycle — is not a nice-to-have in healthcare. It is the front line of breach prevention.
A large health system in 2026 runs an Electronic Health Record platform, a billing system, a PACS for imaging, a pharmacy management tool, a credentialing platform, a patient portal, and likely dozens of integrated SaaS applications. Many of these systems were deployed in different eras, by different teams, with different authentication standards.
Managing identity and access across this environment without a unified governance framework means managing dozens of separate credential stores, access policies that have never been reconciled against each other, and audit trails that exist in silos. When a regulator asks who had access to what on a given date, the honest answer is often: we are not entirely sure.
By 2026, non-human identities, including APIs, bots, IoT devices, and third-party integrations, are projected to outnumber human users by more than 3 to 1 in large enterprises. In healthcare, this means connected monitors, diagnostic equipment, lab analyzers, remote patient monitoring devices, and integration engines all carry digital identities that need to be governed, managed, and monitored. Unmanaged machine identities create silent, persistent attack paths that traditional perimeter security was never designed to detect.
For healthcare CISOs and compliance officers who have been treating IAM as an aspirational project, 2026 has arrived with a new sense of urgency.
The Office for Civil Rights has confirmed that its HIPAA enforcement priorities in 2026 will expand beyond risk analysis to include risk management, meaning organizations must now demonstrate not only that they identified risks but that they actively reduced them in a timely manner. OCR closed 22 HIPAA investigations with financial penalties in 2024 alone. The enforcement trajectory is upward.
Simultaneously, the updated HIPAA Security Rule amendments pending review in 2026 include explicit requirements for multi-factor authentication, network segmentation, and role-based access controls, controls that map directly to a mature IAM framework. Organizations that have invested in building structured IAM governance are positioned to demonstrate compliance without the last-minute remediation cycles that drain IT teams and create audit exposure. Organizations that have not invested are running out of road.
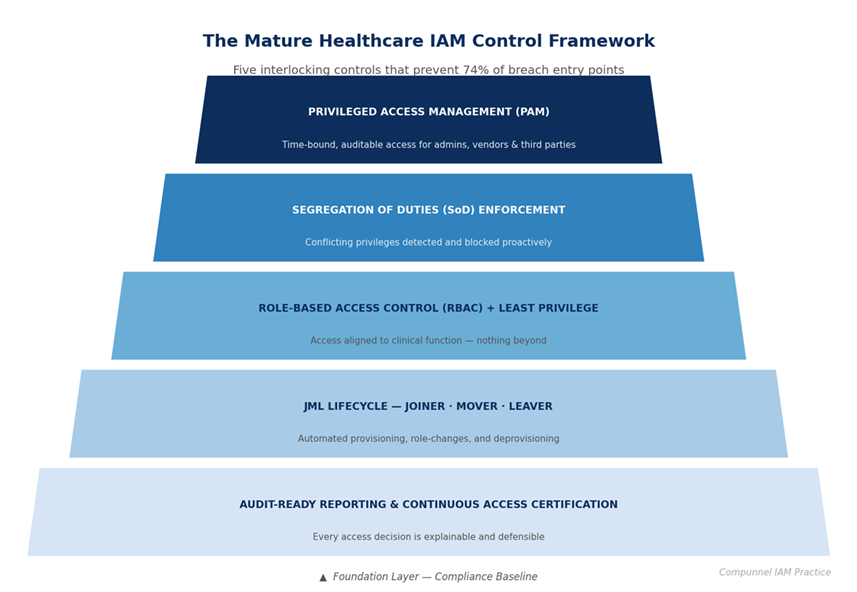
The gap between a compliant healthcare organization and a vulnerable one is not a million-dollar technology investment. It is a governance decision. Mature IAM programs in healthcare share a consistent set of structural characteristics:
Healthcare organizations evaluating IAM strategy in 2026 are not just buying a technology platform. They are selecting a partner accountable for governing identity risk across one of the most complex, regulated, and targeted environments in the digital world.
Compunnel’s Identity and Access Management services are built specifically for this accountability. As part of a broader portfolio of enterprise cybersecurity services, Compunnel’s IAM practice brings 30 years of enterprise delivery, 10 million governed identities, and certified expertise across the platforms healthcare organizations actually run: Microsoft Entra ID, Okta, SailPoint, Saviynt, CyberArk, and ObserveID.
The Compunnel healthcare IAM framework addresses the full lifecycle. Governance establishes policies and controls across the workforce, contractor, and third-party identities. Automated JML ensures access is granted on day one, adjusted as roles shift, and revoked without delay. RBAC aligns permissions to clinical and operational functions. SoD enforcement prevents conflicting access before it becomes an audit event. And 24/7 managed services support means the program does not degrade between review cycles.
For healthcare CISOs whose budgets are finite and whose threat landscape is not, Compunnel’s approach delivers 50% faster provisioning, 80% reduction in manual access work, and the audit-ready documentation trail that turns a regulator inquiry from a crisis into a conversation.
McLaren Health Care’s story does not have to be your organization’s story. But avoiding it requires a decision, made now, about whether identity governance is infrastructure or an afterthought.
Is Your Healthcare IAM Program Audit-Ready, Breach-Ready, and Operationally Sound?
Find out in 30 minutes. Compunnel’s IAM specialists work exclusively in healthcare-scale identity environments. No generic demos, no sales scripts. A real conversation about where your access risk lives and how to close it.
