The Hospital That Got Hacked Twice in One Year Had the Same Problem Both Times
Meet the Hospital That Paid Twice for the Same Mistake In August 2024, Michigan's McLaren Health Care went dark. Ransomware.…
Think of it as digital sediment. Every employee who joined and never had access to a properly scoped environment. Every contractor whose project ended, but whose credentials did not. Every administrator whose role changed six months ago, but whose original privileges traveled with them. Every vendor login that was provisioned for a system upgrade has never revoked.
It accumulates quietly, invisibly, and at a rate most healthcare IT teams genuinely do not track. The technical term is orphaned access. The operational reality is an attack surface that grows every day your workforce turns over, your systems change, and your IAM processes fail to keep pace.
And healthcare workforces turn over constantly. The Bureau of Labor Statistics reports voluntary turnover in nursing at approximately 22% annually. In a health system of 5,000 clinical and administrative staff, there are 1,100 leavers a year. If just 20% of those former employees retain residual access to any system for any period after departure, you are managing over 200 active credentials attached to people who no longer work for you. And that is before counting contractors, per-diem staff, students on rotation, and the third-party vendors whose service personnel cycle through your environment on schedules nobody in IT fully controls.
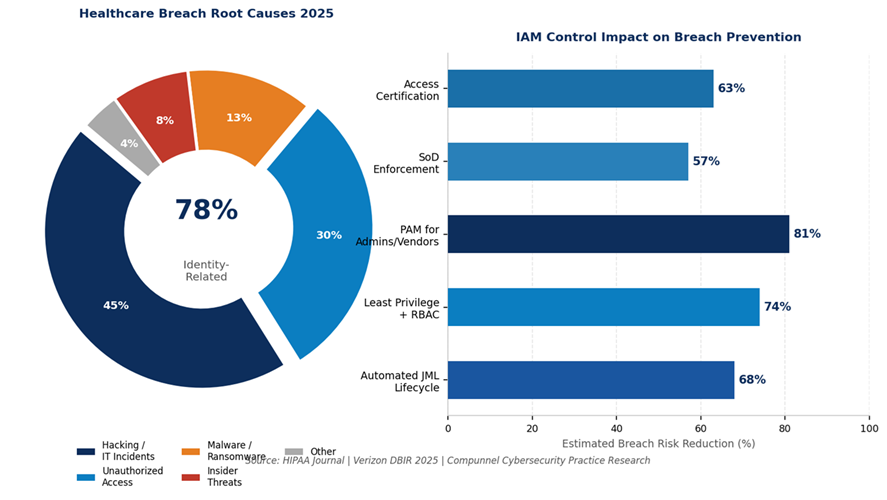
Unauthorized access and disclosure in healthcare grew 240% in 2025 compared to 2024, according to Fortified Health Security’s annual report covered by TechTarget. The largest contributors: misdirected communications, improper internal access, and shadow AI risks. These are not exotic threat vectors. They are governance failures. They are what happens when the Joiner, Mover, Leaver process breaks down.
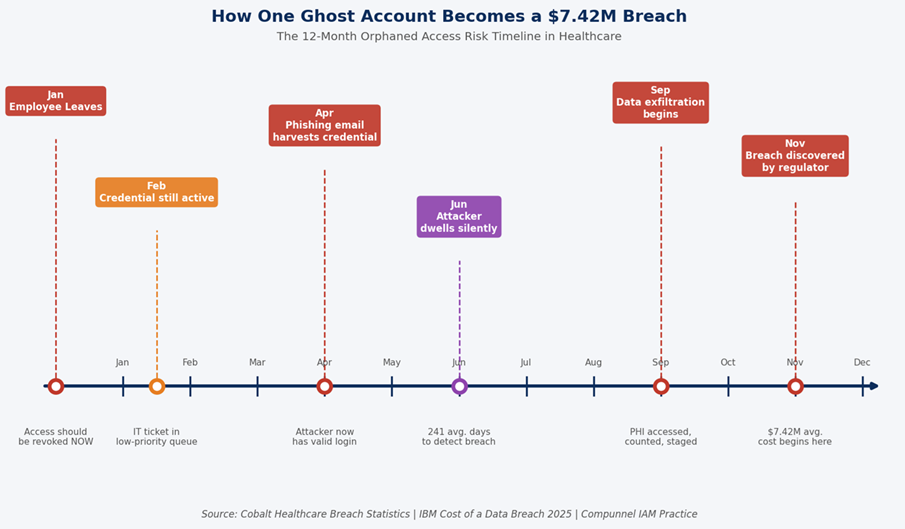
Let us describe a scenario that is neither rare nor sensationalized.
A traveling nurse completes a 13-week assignment at a large regional hospital system. IT receives the termination notice. The payroll record is closed. But the nurse’s credentials to the EHR, the scheduling platform, and two ancillary clinical applications remain active. Nobody flagged the third-party staffing arrangement in the provisioning workflow. The deprovisioning ticket was created, but assigned to a queue that processes tickets in order of priority, and a termination for a contractor does not automatically trigger high priority.
Sixty days later, those credentials are still live. They are not being used by the nurse. But they exist. They are indexed in your identity store. They represent access to Protected Health Information. And if a phishing campaign harvests them from a personal email account the nurse used for a forgotten password reset six months ago, they become the key that opens your records to an attacker who can dwell undetected for months.
This is not hypothetical architecture. It is the breach pattern that cybersecurity expert Dave Bailey at Clearwater described for 2026: identity-centric intrusions that let attackers stay undetected long enough to perform extensive reconnaissance and data theft. The point of entry is not a zero-day exploit. It is a ghost account your offboarding process missed.
Healthcare compliance officers who treat IAM as an IT problem rather than a governance problem are about to encounter a significant reframe.
The HHS Office for Civil Rights has been explicit about its 2026 enforcement expansion. Following years of escalating HIPAA penalties, OCR is now requiring organizations to demonstrate active risk management, not merely risk identification. That distinction matters enormously in the context of access governance. Documenting that excessive privilege is a risk while continuing to allow it is no longer a defensible compliance posture. Demonstrating that you identified excessive privilege, implemented Role-Based Access Controls, and can produce an audit trail of every access decision and certification cycle, is.
The financial stakes have never been higher. A 2025 settlement saw the New York Attorney General impose a $500,000 penalty on a single orthopedic practice for cybersecurity failures affecting 656,086 patients. The largest settlement in HIPAA history reached $16 million. And every year, OCR processes hundreds of investigations where inadequate access controls are among the primary identified violations.
Here is the part that does not always make it into the security briefing: Poor identity and access management does not just create breaches. It creates operational friction that costs clinical organizations time and money every single day.
The average hospital clinician interacts with between seven and fifteen applications during a standard shift. Each application historically demanded a separate login. Each forgotten password triggered a helpdesk ticket. Nurses who are mid-procedure cannot pause to reset credentials. Physicians pulling an urgent record cannot wait for IT to restore access. The friction is not just annoying. It is a patient safety issue.
Single Sign-On, properly implemented as part of a mature IAM framework, eliminates this friction entirely. Role-based access means clinicians see exactly what they need for their function. Provisioning processes mean access is ready on day one. This is not cybersecurity at the expense of usability. It is cybersecurity that makes clinical work faster and safer simultaneously.
While previous years focused on the careless user as the weak link, cybersecurity professionals heading into 2026 have shifted attention. As one expert quoted by BankInfoSecurity put it, it is time to start focusing on the careless system administrator. In smaller hospitals and clinics, IT staff handling user provisioning and cloud environment setup often lack certifications or formal training in those areas. Microsoft 365 configuration errors, improperly scoped admin privileges, and misconfigured Azure environments are creating vulnerabilities that no perimeter firewall can compensate for.
Privileged Access Management solves this structurally. By enforcing time-bound, auditable access for system administrators, vendors, and contractors, PAM ensures that the most powerful credentials in the environment are also the most carefully governed. When a privileged session occurs, it is logged, monitored, and defensible. When it ends, the access ends with it.
In 2025, cybersecurity experts documented a clear trend: adversaries are increasingly targeting third-party technology providers precisely because breaching one widely deployed platform can open the door to dozens or hundreds of healthcare organizations. Revenue cycle management vendors, clinical IT support providers, and SaaS application administrators all require access to your systems, but are often governed under informal processes that do not meet the standards applied to direct employees.
A mature IAM framework extends governance to every identity type: employee, contractor, vendor, machine, and application. It assigns each a digital identity, scopes access to what is genuinely required, governs the lifecycle of that access, and terminates it with the same precision applied to full-time employees on their last day.
The characteristics of a healthcare IAM program that actually prevents these scenarios are not exotic. They are methodical.
Healthcare organizations that have attempted to build IAM governance internally often reach the same conclusion: the complexity of the clinical environment, the diversity of the technology stack, and the pace of workforce change exceed what any internal team can govern effectively without a purpose-built framework and a partner who has done it before, at scale, in regulated environments.
Compunnel’s Identity and Access Management services have governed more than 10 million identities across healthcare and regulated enterprise environments. The practice holds certified expertise across every major IAM platform healthcare organizations operate, including Microsoft Entra ID, Okta, SailPoint, Saviynt, and CyberArk, and delivers in a platform-agnostic model that works within the architecture you already have.
The Compunnel healthcare IAM framework is not a technology installation. It is a governance program: policies, controls, automated lifecycle management, continuous compliance monitoring, and 24/7 managed services support that keeps your identity environment governed between review cycles and audits.
As part of Compunnel’s broader enterprise cybersecurity services capability, the IAM practice sits within a full security architecture that connects identity governance to endpoint security, cloud security, data protection, and security operations. Because identity is not a standalone discipline, it is the control plane through which every other security decision in your environment flows.
The ghost accounts are already in your system. The question is whether you find them before an attacker does.
Find Out Exactly Where Your Access Governance Gaps Are before Anyone Else Does.
Compunnel’s healthcare IAM specialists offer a 30-minute discovery consultation that maps your current identity lifecycle controls against the patterns that drive 2026 breaches. No commitment. No sales pitch. Just clarity.
